European cybersecurity officials will call on national governments to impose stricter limits on telecom operators and partial bans on high risk suppliers, according to a new document on 5G security seen by POLITICO.
The officials plan to present their recommendations as part of a new security “toolbox” next week which includes a range of measures that aim to stop 5G networks from being hacked, disrupted or spied upon by foreign governments.
The measures do not mention Chinese 5G equipment maker Huawei by name. But the list of recommended actions would allow EU capitals to limit Huaweis role in 5G networks across the Continent in coming years.
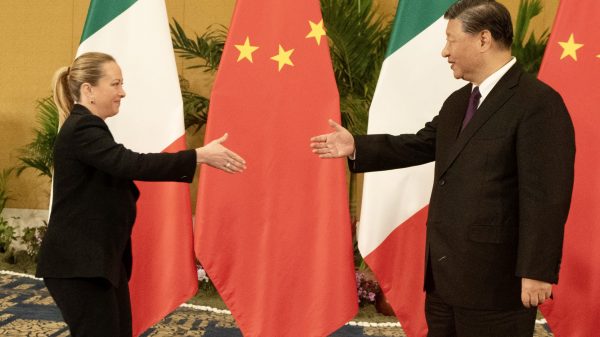
The plans are the latest — and arguably strongest — move by European lawmakers to reshape the EU-China relationship ahead of two critical summits this year that will feature discussions on trade tensions, technology and competition practices.
They mark the culmination of work on stricter 5G security rules that began in early 2019, following strong calls by U.S. officials about the risks associated with Huawei. The company denies posing any security risk.
Countries including France, the Netherlands and Italy have already beefed up their rules on telecom security, while Germany and the United Kingdom are in the midst of reviewing their rules amid intense public debate about Huaweis role.
The “toolbox” follows an earlier warning in October by the same cybersecurity expert group that state-backed hacking groups are a major threat to the security of 5G networks — implicitly pointing to China and Chinese vendors as bearing a higher risk for European telecom operators.
In a “5G Risk Assessment” report, first reported by POLITICO, the Commissions group of experts then said suppliers may be more risk-prone if there is a higher “likelihood of the supplier [of 5G network gear] being subject to interference from a non-EU country” through intelligence legislation, government control of a companys management or a lack of “democratic checks and balances in place” to counter such espionage attempts.
In its new “toolbox” document, the cybersecurity experts in the NIS Cooperation Group — a forum for cybersecurity cooperation between European officials — urged EU capitals to take urgent steps to beef up network security and to minimize “the exposure to risks stemming from the risk profile of individual suppliers.”
The group includes representatives of national cybersecurity authorities, as well as members of the EUs Cybersecurity Agency ENISA and the European Commission.
While the groups recommendations are nonbinding, they are likely to push European governments to review and beef up their national security measures in the short term.
The toolbox is expected to be presented next week Wednesday in Brussels, together with a Commission “communication” document that sets out the EUs view on how to move forward with the measures.
Exclusions
The “toolbox” document calls for capitals to apply new “restrictions — including necessary exclusions” on “critical or sensitive” parts of 5G networks. Those parts include core networks, network management functions and parts of the core networks that manage data traffic to base stations and antennas, the experts said.
While this would mean Huawei could face new significant market restrictions, it would not exclude the Chinese vendor from selling base stations and antennas in Europe right now. Such sales of so-called Radio Access Network equipment make up the lions share of 5G profits for suppliers.
New measures would also impose stricter rules on whether foreign companies can provide services to Europes network operators in the future, as telecom networks become more reliant on software.
Those restrictions and potential exclusions are targeted at “high-risk” vendors, which the EU previously defined as suppliers likely to be “subject to interference from a non-EU country,” the document said, and that are expected to include Huawei and its smaller Chinese rival ZTE.
The European cybersecurity experts are calling on national authorities to impose such limits.
But they stopped short of naming the high-risk vendors or clearly stipulating how national security agencies would name them.
Audits
The group also called on capitals to take a much stronger role in overseeing the security of telecom networks.
That would include setting up mechanisms to scrutinize private contracts between operators and their suppliers and setting up “audits” of telecom companies to check their security policies and “multi-vendor strategies.”
The document calls for “technical” measures including imposing baseline security policies, managing access of employees or contractors, updating and patching software, imposing stricter requirements on suppliers that procure gear and services and creating a certification scheme for 5G network components.
The group also called for pan-European measures, including setting up a review mechanism to track how capitals are imposing stricter rules. It said that EU countries should set up perioRead More – Source
[contf] [contfnew] 
politico
[contfnewc] [contfnewc]